Summary
POWERTON is a backdoor written in PowerShell; FireEye has not yet identified any publicly available toolset with a similar code base, indicating that it is likely custom-built. POWERTON is designed to support multiple persistence mechanisms, including WMI and auto-run registry key. Communications with the C2 are over TCP/HTTP(S) and leverage AES encryption for communication traffic to and from the C2. POWERTON typically gets deployed as a later stage backdoor and is obfuscated several layers.
FireEye has witnessed at least two separate versions of POWERTON, tracked separately as POWERTON.v1 and POWERTON.v2, wherein the latter has improved its command and control functionality, and integrated the ability to dump password hashes.
SensePost’s RULER is a tool designed to interact with Exchange servers via a messaging application programming interface (MAPI), or via remote procedure calls (RPC), both over HTTP protocol. As detailed in the “Managed Defense Rapid Responses” section, in mid-November 2017, FireEye witnessed network activity generated by an existing Outlook email client process on a single host, indicating connection via Web Distributed Authoring and Versioning (WebDAV) to an adversary-controlled IP address 85.206.161[.]214. This communication retrieved an executable created with Aut2Exe (MD5: 95f3bea43338addc1ad951cd2d42eb6f), and executed a PowerShell one-liner to retrieve further malicious content.
Indicators of Compromise
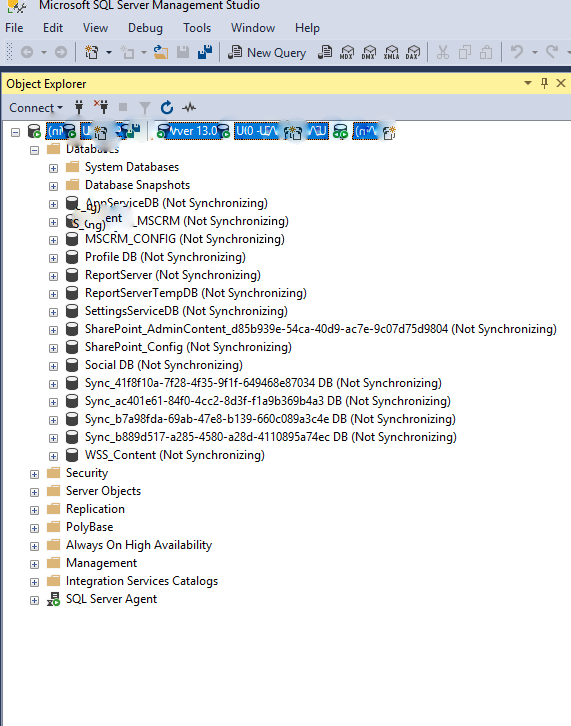
| Hash of Obfuscated File (MD5) | Hash of Deobfuscated File (MD5) | Version |
| 974b999186ff434bee3ab6d61411731f | 3871aac486ba79215f2155f32d581dc2 | V1 |
| e2d60bb6e3e67591e13b6a8178d89736 | 2cd286711151efb61a15e2e11736d7d2 | V1 |
| bd80fcf5e70a0677ba94b3f7c011440e | 5a66480e100d4f14e12fceb60e91371d | V1 |
| 4047e238bbcec147f8b97d849ef40ce5 | f5ac89d406e698e169ba34fea59a780e | V2 |
| c38069d0bc79acdc28af3820c1123e53 | 4aca006b9afe85b1f11314b39ee270f7 | V2 |
| N/A | 7f4f7e307a11f121d8659ca98bc8ba56 | V2 |
| 53ae59ed03fa5df3bf738bc0775a91d9 | 99649d58c0d502b2dfada02124b1504c | V2 |
Recommendations
• Ensure to have the latest patches of Microsoft Outlook installed.
• Restrict PowerShell execution.